Cyber Smart Week – Upholding your privacy online
Upholding your privacy online is increasingly important. Most of us know someone who has had a Facebook account hacked or their identity impersonated via fake accounts or phishing emails.
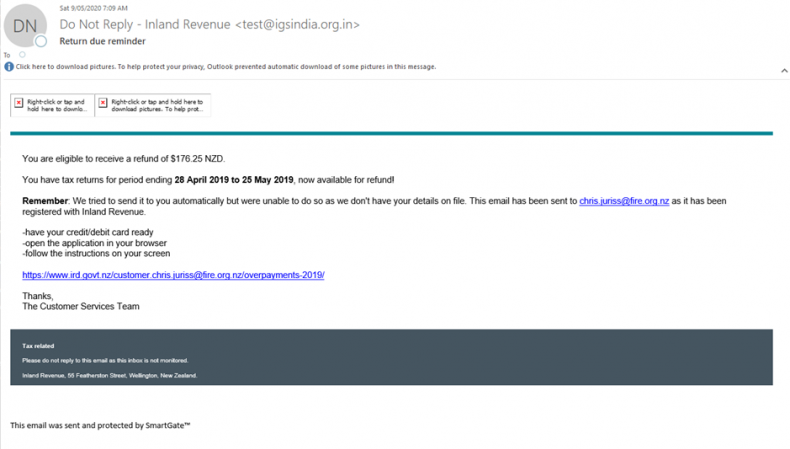
At Fire and Emergency, our systems are threatened by phishing emails almost every day. Although most are stopped - by using personal information, they are becoming more sophisticated and harder to spot.
For example, a recent FluBot malware threat used text messages to try and convince you to click on a link to receive a delivery. These texts looked legitimate at first glance - but were you expecting a delivery? If in doubt, never click on anything.
 You can always check its legitimacy by contacting the organisation through their contact centre or email. It is highly unlikely that any organisation will ask you for personal information directly via text or email.
You can always check its legitimacy by contacting the organisation through their contact centre or email. It is highly unlikely that any organisation will ask you for personal information directly via text or email.
The more information you share, the easier it is for attackers to impersonate you online or even try to steal your identity.
By upholding your privacy and creating good habits around what information you share on personal accounts - you can enhance your security and reduce the risk of your personal information being used for malicious activities against Fire and Emergency and other organisations.
Our advice:
- Keep a check on what information you’re sharing online, and who you’re sharing it with. We’re so used to sharing things online that we don’t always take a moment to think about how it affects our privacy.
- Check that the privacy settings on your social media accounts are set to ‘Friends Only’ or private, so only those you know can see what you’re up to.
- When signing up for a new online account, provide only the information required for it to be functional for you. Do they need to know your middle name and phone number?
- If you suspect you've received a suspicious email or text, don't click on anything. Contact the organisation through their official channels.
- If you think you've received a phishing email, follow these steps
- And read ICT's acceptable use policy here
- You can also check out CERT NZ’s guide to protecting your privacy(external link)
Phishing email examples